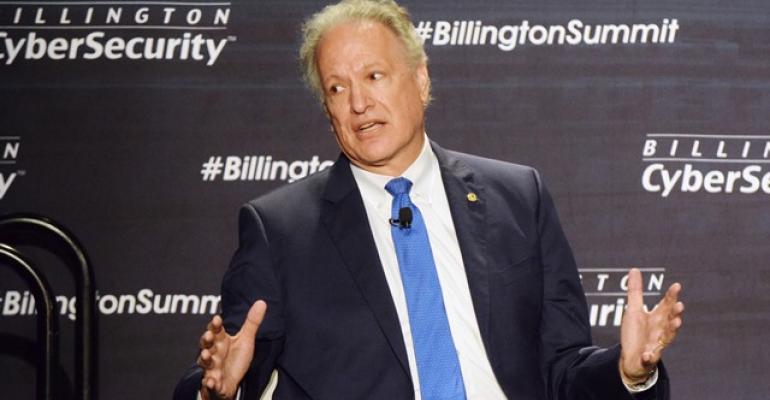
DETROIT – NHTSA Administrator Mark Rosekind says he understands the safety threat posed by hackers as automakers veer toward self-driving cars in the future, and he supports expanded collaboration between the industry and government to fight it.
“There are 265 million vehicles out there now,” and the potential for vulnerabilities will increase as new mobility models, such as ride sharing, take hold, Rosekind says on a panel discussion during the Billington Global Automotive Cybersecurity Summit, held here at Cobo Center.
“If we have connected vehicles and all kinds of automation out there, each one of those is a vulnerability,” he says.
Government and the industry must be “nimble and flexible” in heading off issues before they impact public safety, but Rosekind says Washington has a poor track record on that front, noting it took 16 years to adopt regulations for enhanced airbags, rear visibility cameras and electronic stability control.
“That’s not nimble and flexible,” he says.
The safety of U.S. roads and highways must not be compromised by hackers, Rosekind says, referring to 35,200 fatal accidents in 2015. “And 94% of those were due to human choice or error. That’s the context for all of this discussion.”
Even in the face of cyber-threats, the auto industry and government must not let up in developing automated and connected vehicles, Rosekind says.
“With all that great technology comes the vulnerabilities. We know there are bad actors looking for ways to compromise the life-saving potential that’s out there with automated and connected vehicles,” he says. “This is an issue where the government and industry are lined up 100%. This is a place where there are no conflicts.”
In her morning keynote address, General Motors CEO Mary Barra says there will be about 50 billion smart devices around the world by 2020 and 41 global megacities, each home to more than 10 million people, up from 28 today.

“Each of these trends is reflected in today’s global auto industry,” Barra says. “In fact, I fully expect the auto industry to change more in the next five years than it has in the last 50.”
For instance, vehicles are growing increasingly complex. In 2000, cars had, on average, about 1 million lines of code, she says.
“The first generation Chevrolet Volt, which was introduced in late 2010, had about 10 million lines of code – which is more than an F-35 fighter jet,” Barra says. “Today, an average car has more than 100 million lines of code, and it won’t be long before it’s 200 million.”
This makes fertile ground for hackers.
“Sophisticated attacks are specifically designed to circumvent even the most robust defense systems,” she says. “Whether it is phishing or spyware, malware or ransomware, the attacks are getting more and more sophisticated every day.”
GM is among several automakers that created the Automotive Information Sharing and Analysis Center a year ago to promote collaboration in improving cybersecurity.
This week, the Auto-ISAC issued an executive summary highlighting “best practices” to be shared among member companies in the bid to prevent dangerous hacks.
Sharing Best Practices, 'Don't Keep Secrets'
Those best practices, meant to be aspirational stretch targets, include threat detection, incident response, training and collaboration with appropriate third parties, as well as:
- Defining executive oversight for product security.
- Functionally aligning an organization to address vehicle cybersecurity, with defined roles and responsibilities across the organization.
- Communicating oversight responsibility to all appropriate internal stakeholders.
- Dedicating appropriate resources to cybersecurity activities across the enterprise.
- Establishing governance processes to ensure compliance with regulations, internal policies, and external commitments.
GM will continue supporting Auto-ISAC and will endorse all recommendations in the executive summary.
“And we commit to implementing the actions and best practices outlined in the document,” Barra says. “A cyber incident is not a problem just for the automaker involved. It is a problem for every automaker around the world.”

Automakers are used to competing with each other, not collaborating. Still, the Auto-ISAC is making solid progress, says Bently Au, chief information security officer-Enterprise Information Security Program at Toyota Motor Sales USA.
“Maybe there was some doubt about how fast or how much we could do,” Au says. “But I think we’ve been successful at moving, frankly, a lot quicker than even I thought we would. I think it’s impressive.”
Suppliers can help the cause of cybersecurity, says Steven Center, vice president-
Environmental Business Development at American Honda.
Suppliers, especially member companies within Auto-ISAC, must come forward when they detect any threat.
“Don’t keep any secrets,” Center says. “It only gets worse.”

Jeffrey Massimilla, GM’s chief product cybersecurity officer, agrees.
“If you see things in your environment, you should be reporting it through the information sharing portal,” he says. “It might not even affect a manufacturer, but that doesn’t mean it shouldn’t be reported.”
Josh Corman, founder of I Am The Cavalry and director of the Atlantic Council of the Cyber Statecraft Initiative, also serves on the Auto-ISAC and doubts the industry can create a vehicle that is 100% hack-proof.
“We have a window of exposure that we need to close very, very quickly,” he says.